Key highlights of semiannual Global Threat Landscape Report from FortiGuard Labs
Fortinet, the global cybersecurity leader driving the convergence of networking and security, recently announced the latest semiannual Global Threat Landscape Report from FortiGuard Labs. The threat landscape and organizations’ attack surface are constantly transforming, and cybercriminals’ ability to design and adapt their techniques to suit this evolving environment continues to pose significant risk to businesses of all sizes, regardless of industry or geography.
Commenting on this report, Vishak Raman, Vice President of Sales, India, SAARC & Southeast Asia at Fortinet said; “For cyber adversaries, maintaining access and evading detection is no small feat as cyber defenses continue to advance to protect organizations today. To counter, adversaries are augmenting with more reconnaissance techniques and deploying more sophisticated attack alternatives to enable their destructive attempts with APT-like threat methods such as wiper malware or other advanced payloads. To protect against these advanced persistent cybercrime tactics, organizations need to focus on enabling machine learning–driven coordinated and actionable threat intelligence in real time across all security devices to detect suspicious actions and initiate coordinated mitigation across the extended attack surface.”
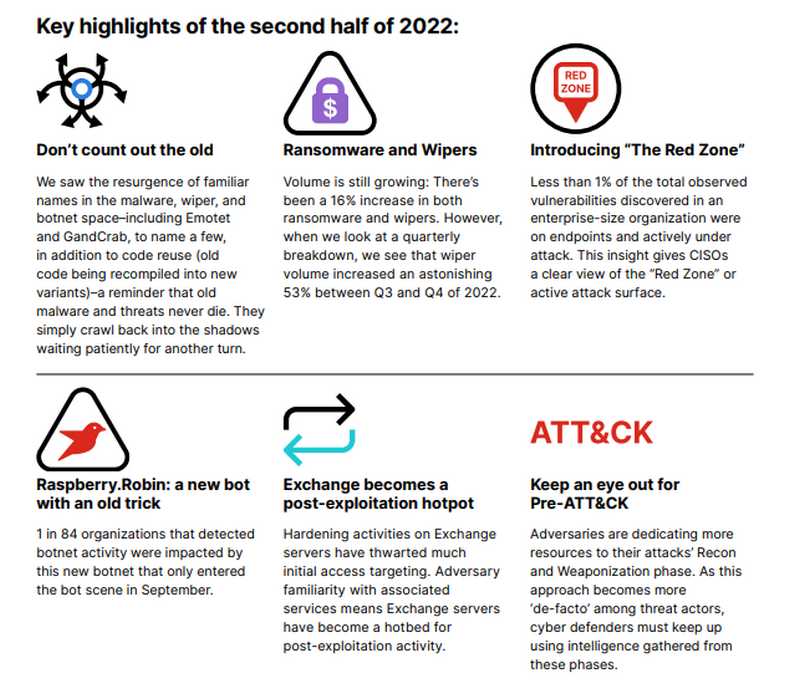
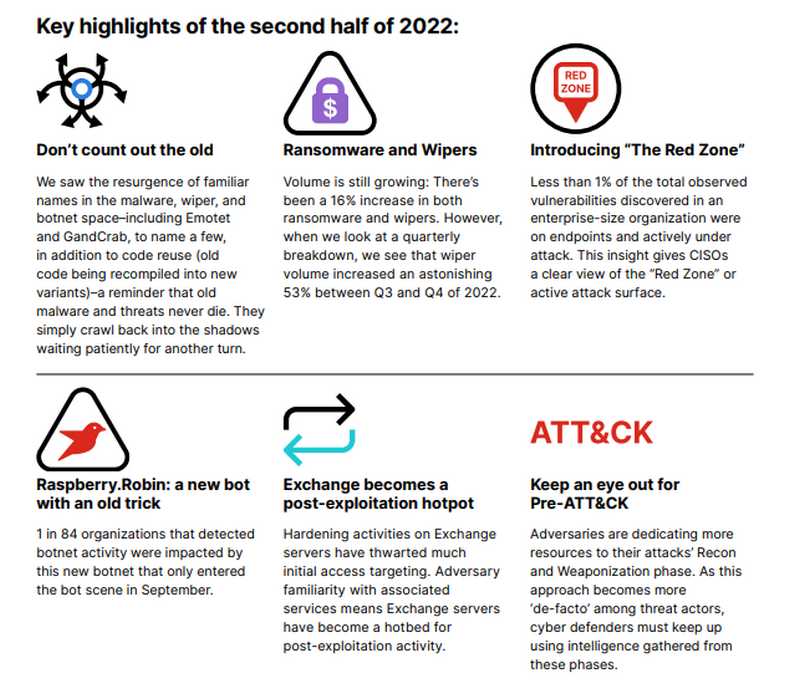
Highlights of the 2H 2022 report follow:
- The mass distribution of wiper malware continues to showcase the destructive evolution of cyberattacks.
- New intelligence allows CISOs to prioritize risk mitigation efforts and minimize the active attack surface with the expansion of the “Red Zone” approach.
- Ransomware threats remain at peak levels with no evidence of slowing down globally with new variants enabled by Ransomware-as-a-Service (RaaS).
- The most prevalent malware was more than a year old and had gone through a large amount of speciation, highlighting the efficacy and economics of reusing and recycling code.
- Log4j continues to impact organizations in all regions and industries, most notably across technology, government, and education.
Destructive APT-like Wiper Malware Spreads Wide in 2022
Analyzing wiper malware data reveals a trend of cyber adversaries consistently using destructive attack techniques against their targets. It also shows that with the lack of borders on the internet, cyber adversaries can easily scale these types of attacks, which have been largely enabled by the Cybercrime-as-a-Service (CaaS) model.
Mapping CVEs Reveals Vulnerability Red Zone to Help CISOs Prioritize
Exploit trends help show what cybercriminals are interested in attacking, probing for future attacks, and are actively targeting. FortiGuard Labs has an extensive archive of known vulnerabilities, and through data enrichment was able to identify actively exploited vulnerabilities in real time and map zones of active risk across the attack surface.
In the second half of 2022, less than 1% of the total observed vulnerabilities discovered in an enterprise-size organization were on endpoints and actively under attack, giving CISOs a clear view of the Red Zone through intelligence of the active attack surface that they should prioritize efforts to minimize their risk and where to focus patching efforts.
Financially Motivated Cybercrime and Ransomware Threat Holding at Peak Levels
FortiGuard Labs Incident Response (IR) engagements found that financially motivated cybercrime resulted in the highest volume of incidents (73.9%), with a distant second attributed to espionage (13%). In all of 2022, 82% of financially motivated cybercrime involved the employment of ransomware or malicious scripts, showing that the global ransomware threat remains in full force with no evidence of slowing down thanks to the growing popularity of Ransomware-as-a-Service (RaaS) on the dark web.
Adversary Code Reuse Showcases the Resourceful Nature of Adversaries
Cyber adversaries are enterprising in nature and always looking to maximize existing investments and knowledge to make their attack efforts more effective and profitable. Code reuse is an efficient and lucrative way for cybercriminals to build upon successful outcomes while making iterative changes to fine-tune their attacks and overcome defensive obstacles.
Older Botnet Resurrection Demonstrates the Resiliency of Adversarial Supply Chains
In addition to code reuse, adversaries are also leveraging existing infrastructure and older threats to maximize opportunity. When examining botnet threats by prevalence, FortiGuard Labs discover that many of the top botnets are not new. For example, the Morto botnet, which was first observed in 2011, surged in late 2022. And others like Mirai and Gh0st.Rat continue to be prevalent across all regions. Surprisingly, out of the top five observed botnets, only RotaJakiro is from this decade.
Log4j Remains Widespread and Targeted by Cybercriminals
Even with all the publicity that Log4j received in 2021 and the early parts of 2022, a significant number of organizations still have not patched or applied the appropriate security controls to protect their organizations against one of the most notable vulnerabilities in history.
Analyzing a Piece of the Malware Story: Delivery Shifts Demonstrate Urgency for User Awareness
Analyzing adversarial strategies gives us valuable insights into how attack techniques and tactics are evolving to better protect against future attack scenarios. FortiGuard Labs looked at the functionality of detected malware based on sandbox data to track the most common delivery approaches. It is important to note that this only looks at detonated samples.
Shifting to Meet the Threat Landscape Head-On
Fortinet is a leader in enterprise-class cybersecurity and networking innovation, helping CISOs and security teams break the attack kill chain, minimize the impact of cybersecurity incidents, and better prepare for potential cyberthreats.